An arbitrary file upload vulnerability in the upload payment plugin of ShopXO v1.9.0 allows attackers to execute arbitrary code via uploading a crafted PHP file.
Vulnerability Analysis
A vulnerability is a weakness in an information system, system security procedures, internal controls, or implementation that could be exploited or triggered by a threat source.
NIST Glossary – https://csrc.nist.gov/glossary/term/vulnerability
Vulnerability analysis includes the detection, assessment, classification and treatment based on the risk they pose to the company.
Vulnerability Identification
A security team can detect vulnerabilities following different approaches. As part of a vulnerability management process, it is good practice to subscribe to the mailing lists in which vulnerabilities and related countermeasures are disclosed. This service is usually offered by the vendor or, if not available, through third parties. It is a very time expensive but necessary task. You must perform it on a daily basis to promptly detect vulnerabilities and to comply with several standards/regulations.
Other inputs could derive from the analysis of the hardening procedures reports/tasks, the periodic review of the access rules and of the company policies and procedures.
Tools
Thanks to tools like Nessus and OpenVAS, it is possible to partially automate the discovery and analysis of vulnerabilities. After verifying the active hosts and the related services, we can deepen our analysis and determine the operating system and application versions.
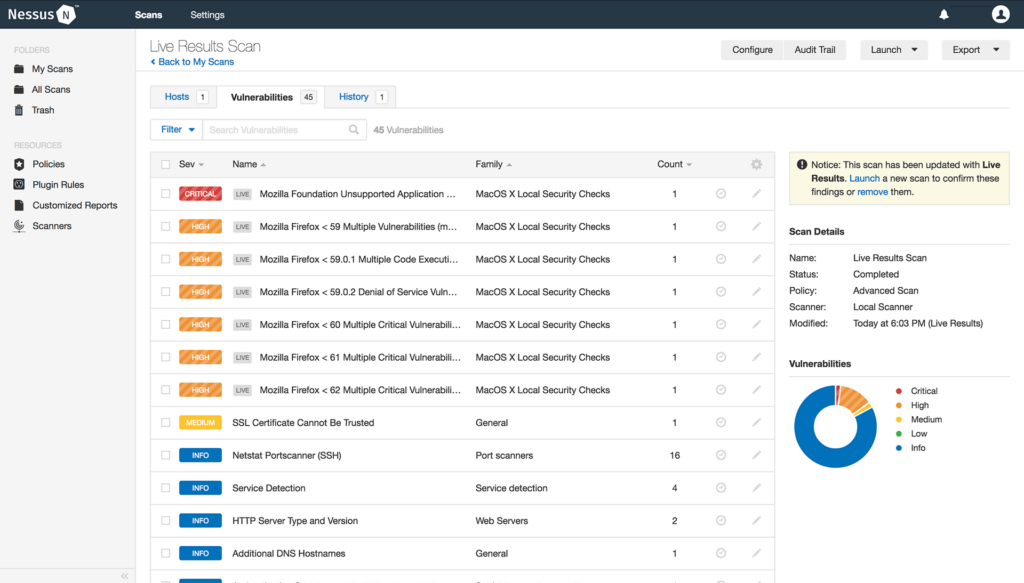
As shown in the figure, Nessus provides the list of vulnerabilities to which each analyzed host is potentially vulnerable. Potentially because the scanner does not attempt to exploit the vulnerability. This phase, often manual, is not part of the vulnerability analysis process and is normally carried out within a penetration test.
CVSS
In the report, vulnerabilities are classified according to the CVSS (Common Vulnerability Scoring System), a framework used to classify software vulnerabilities. CVSS is an important tool that simplifies the vulnerability management process.
Let’s pretend you are in a meeting with the company management and you have to share the results of your vulnerability analysis. The test results were not good: you need at least three system administrators for one month to implement the remediation plan. You need to install patches, implement countermeasures, and you have to do it fast. During the meeting, you could try to tell management that you found several RCE-type vulnerabilities on systems deployed in your DMZ. Attackers do not need system/applications credentials to perform the attack and exploits are readily available on the Internet. Or you could report the presence of several CVSS 10 vulnerabilities on critical systems.
For more information on CVSS, in its two versions 2.0 and 3.0, I suggest reading our article.
CVE & NVD
Each vulnerability has a Common Vulnerability and Exposures (CVE) ID, in the form of CVE-YYYY-NNNN. The assignment of an ID to each vulnerability allows one to keep track of it and to automate/simplify the integration of the different tools available to an analyst.
Let’s say you have just detected a vulnerability on your firewall appliance. Since it is a well-known vulnerability, it has got a specific CVE-ID. Assuming that your firewall vendor catalogues their vulnerabilities and patches by CVE, it is going to be easy to ask the vendor for additional information, search for the relevant patches and to minimize the possible impacts of applying remediation on the infrastructure. Furthermore, it is going to be easy to find the relevant signature in your IDS/IPS.
CVE is operated by “The Mitre Corporation“. More details can be obtained on the cve.org website.
NVD (National Vulnerability Database) is managed by NIST (National Institute of Standards and Technology). NVD is a vulnerability database: for each CVE information such as countermeasure, criticality and impact is provided.
CWE & OWASP
CWE (Common Weakness Enumeration) is a list of common types of hardware and software defects that have security implications. The CWE list can be used as a framework to describe and communicate such vulnerabilities in terms of CWEs. The CWE Top 25 Most Dangerous Software Weakness List is a list of the most common programming errors that can lead to software vulnerabilities. Vulnerabilities present in the CWE Top 25 are usually easy to detect and exploit. For example, the CWE-79 is related to Cross-Site Scripting while the CWE-89 to SQL Injection. A similar project is Top Ten Owasp (Open Web Application Security Project). Compared to the CWE Top 25, the Top Ten OWASP focuses solely on vulnerabilities of web applications.
The CWE Most Important Hardware Weakness List serves the same purpose, but it focuses on hardware defects.
Vulnerabilty Analysis steps
Vulnerability analysis comprehends different phases.
Preparatory phase
it is not possible to carry out a thorough and reliable analysis without having a deep knowledge of the infrastructure/application under examination. If the procedure for managing IT services and their related assets is not implemented, it is not going to be possible to classify and prioritize vulnerabilities. Let’s say our vulnerability scanner found 300 vulnerabilities on approximately 30 hosts. Which vulnerabilities should I prioritize? Which one shall I remediate immediately? The answer relies not only on the vulnerability severity but also on how important are the hosts and services affected by it.
Discovery and analysis of vulnerabilities
You performed vulnerability scans, you analysed security advisories, system configurations, your company policies and procedures. You have a comprehensive list of vulnerabilities. You can now prioritise them, identify false positives (and false negatives), and improve the results with your knowledge of the infrastructure/application. At the end of this phase, your security team will produce a vulnerability scan report.
Post assessment
It is now possible to define a remediation plan. The remediation plan is not a mere list of the patches, countermeasures and IPS rules: if your analysis has shown the presence of several SQL Injection, CRSF and XSS vulnerabilities in the software developed internally (or by a specific supplier), you must immediately schedule secure programming training classes for your developers.
If these kinds of vulnerabilities are found on software purchased from third parties, you must tell the service owner to look for a new vendor.
While the first scenario is a symptom of a poor security awareness policy, the second one highlights a poor supplier policy: do you review your supplier security policies after you sign a contract? Do you ask to review their development procedures? Do they regularly perform code reviews? Is security fully integrated into their development life-cycle?
Outsourcing has hidden costs that you always need to consider.
Once the remediation plan has been implemented, the security team shall verify it has been properly implemented. Depending on its size, the implementation of the remediation activities can take several weeks, if not months. It is crucial to plan periodic meetings to keep the team focused and to check the progress.
What’s next?
In the next articles, we will analyse the vulnerability management process and its implications for regulations like ISO27001 and PCI-DSS. In the meantime, we suggest reading our articles about CVSS and the Metasploit lab.
Developer sabotages own npm module prompting open-source supply chain security questions
The developer of a popular JavaScript component hosted on the npm repository decided to protest Russia’s invasion of Ukraine by adding code to his own component that would add or delete files on people’s computers in a way they didn’t expect. The component, called node-ipc, is a dependency for a variety of other projects, which had to issue emergency updates to stop the undesired behavior they unwittingly inherited.
It’s the second time something like this has happened this year in the Nodejs community, and some people have started referring to such acts of self-sabotage by developers as protestware. Experts believe that while developers certainly have the right to modify their own software, such acts risk damaging trust in the open-source ecosystem, which has faced increased supply-chain security challenges in recent years.
dotnet3.1-3.1.417-1.fc34
FEDORA-2022-d28042f559
Packages in this update:
dotnet3.1-3.1.417-1.fc34
Update description:
This is the March 2022 update for .NET Core 3.1: SDK 3.1.417 and Runtime 3.1.23
Release notes: https://github.com/dotnet/core/blob/main/release-notes/3.1/3.1.23/3.1.23.md
This includes fixes for CVE-2022-24464, CVE-2022-24512 and CVE-2020-8927
dotnet3.1-3.1.417-1.fc35
FEDORA-2022-5ecee47acb
Packages in this update:
dotnet3.1-3.1.417-1.fc35
Update description:
This is the March 2022 update for .NET Core 3.1: SDK 3.1.417 and Runtime 3.1.23
Release notes: https://github.com/dotnet/core/blob/main/release-notes/3.1/3.1.23/3.1.23.md
This includes fixes for CVE-2022-24464, CVE-2022-24512 and CVE-2020-8927
dotnet3.1-3.1.417-1.fc36
FEDORA-2022-9e046f579a
Packages in this update:
dotnet3.1-3.1.417-1.fc36
Update description:
This is the March 2022 update for .NET Core 3.1: SDK 3.1.417 and Runtime 3.1.23
Release notes: https://github.com/dotnet/core/blob/main/release-notes/3.1/3.1.23/3.1.23.md
This includes fixes for CVE-2022-24464, CVE-2022-24512 and CVE-2020-8927
Friday Squid Blogging: The Costs of Unregulated Squid Fishing
Greenpeace has published a report, “Squids in the Spotlight,” on the extent and externalities of global squid fishing.
News article.
As usual, you can also use this squid post to talk about the security stories in the news that I haven’t covered.
Read my blog posting guidelines here.
New Rootkit Used by UNC2891 for ATM Money Heist
FortiGuard Labs is aware of a report that a threat actor known as UNC2891 used a previously unknown rootkit to capture banking card and PIN verification data from compromised ATM switch servers. The captured data was used to perform fraudulent transactions. Dubbed Caketap, the rootkit allows the threat actor to hide network connections, processes, and files, and install several hooks into system functions to receive commands and configurations from the attacker’s remote server.Why is this Significant?This is significant because the previously unknown Caketap rootkit deployed by the threat actor for Oracle Solaris systems provides stealth for the attacker’s activities and the data it steals can be used for unauthorized financial transactions. The attacks carried out by UNC2891 are financially motivated and could cause great financial damage to the targeted financial institutions. What is Caketap?Caketap is a kernel module rootkit used by UNC2891 on Oracle Solaris systems. The rootkit is used to hide network connections, processes, and files, and install several hooks into system functions to receive commands and configurations from the attacker’s remote server.The rootkit is capable of intercepting certain messages sent for the Payment Hardware Security Module (HSM) in order to disable proper banking card verification and return a valid response to approve fraudulent banking cards. It also examines PIN verification messages. If PIN verification messages are not for a fraudulent banking card, then Caketap does not disrupt valid verification but saves the messages. If Caketap detects PIN verification messages for fraudulent banking cards, it replays the previously saved valid messages for PIN verification bypass.Thales, an HSM vendor, describes the Payment Hardware Security Module (HSM) as “a hardened, tamper-resistant hardware device that is used primarily by the retail banking industry to provide high levels of protection for cryptographic keys and customer PINs used during the issuance of magnetic stripe and EMV chip cards (and their mobile application equivalents) and the subsequent processing of credit and debit card payment transactions”.What is UNC2891?UNC2891 is a threat actor whose main motivation is reportedly for financial gain and has been active for several years. The threat actor is known to not only have extensive knowledge on Oracle Solaris systems, but also Linux and Unix systems.What Other Tools does UNC2891 Use?The following tools are reported to have been used by the threat actor:SLAPSTICK – the Pluggable Authentication Module (PAM) based backdoorCustom version of TINYSHELL – backdoorSTEELHOUND – in-memory dropperSTEELCORGI – in-memory dropperSUN4ME – toolkits that contains tools to spy on network, host enumeration, exploit known vulnerabilities and wipe logsWINGHOOK – keylogger for Linux and Unix systemsWINGCRACK – utility that is used to decode and display the information collected by WINGHOOKBINBASH – ELF utility that executes a shell after the group ID and user ID are set to either “root” or specified valuesWIPERIGHT – ELF utility for Linux and Unix systems and is used to clear specific logsMIGLOGCLEANER – ELF utility for Linux and Unix systems that is used to wipe logs or remove certain strings from logsWhat is the Status of Coverage?FotriGuard Labs provide the following AV coverage:Linux/Agent.T!tr
CVE-2020-25197
A code injection vulnerability exists in one of the webpages in GE Reason RT430, RT431 & RT434 GNSS clocks in firmware versions prior to version 08A06 that could allow an authenticated remote attacker to execute arbitrary code on the system.
CVE-2020-25193
By having access to the hard-coded cryptographic key for GE Reason RT430, RT431 & RT434 GNSS clocks in firmware versions prior to version 08A06, attackers would be able to intercept and decrypt encrypted traffic through an HTTPS connection.