The Internal Revenue Service (IRS) said today it will be transitioning away from requiring biometric data from taxpayers who wish to access their records at the agency’s website. The reversal comes as privacy experts and lawmakers have been pushing the IRS and other federal agencies to find less intrusive methods for validating one’s identity with the U.S. government online.
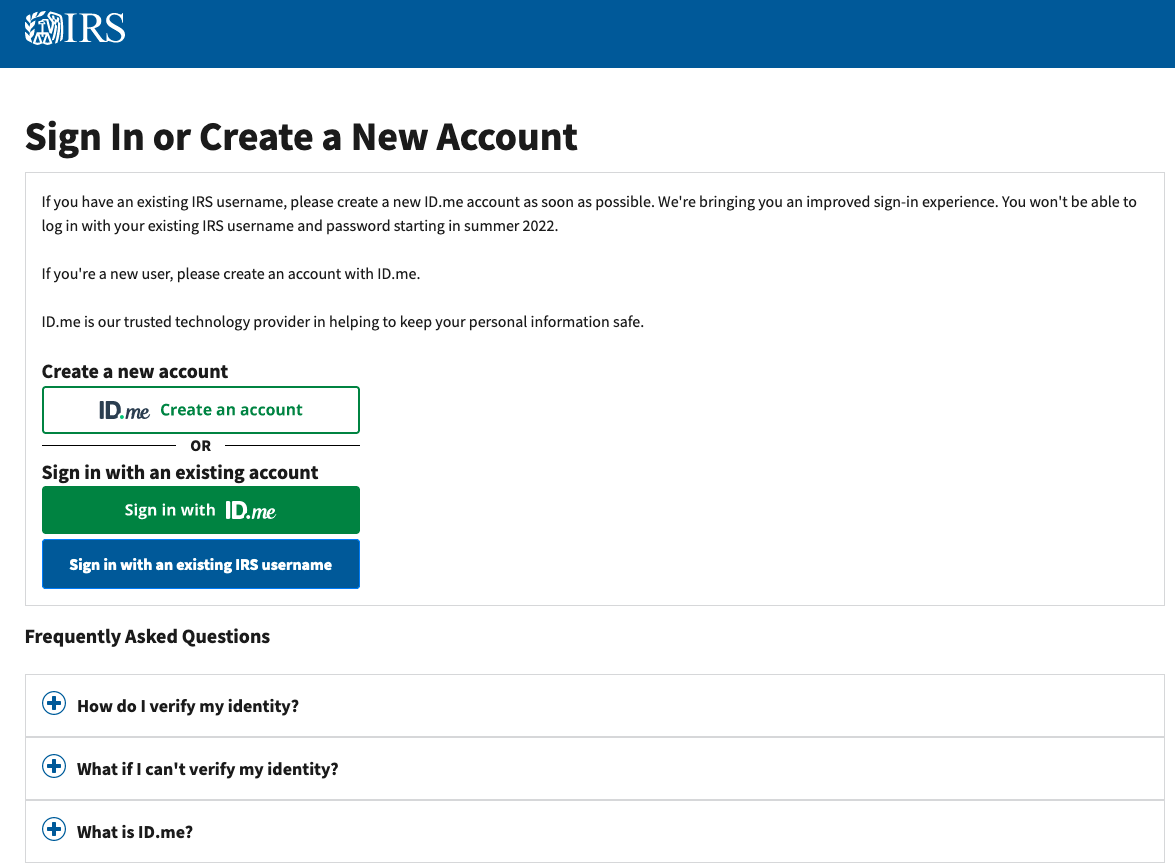
Late last year, the login page for the IRS was updated with text advising that by the summer of 2022, the only way for taxpayers to access their records at irs.gov will be through ID.me, an online identity verification service that collects biometric data — such as live facial scans using a mobile device or webcam.
The IRS first announced its partnership with ID.me in November, but the press release received virtually no attention. On Jan. 19, KrebsOnSecurity published the story IRS Will Soon Require Selfies for Online Access, detailing a rocky experience signing up for IRS access via ID.me. That story immediately went viral, bringing this site an almost unprecedented amount of traffic. A tweet about it quickly garnered more than two million impressions.
It was clear most readers had no idea these new and more invasive requirements were being put in place at the IRS and other federal agencies (the Social Security Administration also is steering new signups to ID.me).
ID.me says it has approximately 64 million users, with 145,000 new users signing up each day. Still, the bulk of those users are people who have been forced to sign up with ID.me as a condition of receiving state or federal financial assistance, such as unemployment insurance, child tax credit payments, and pandemic assistance funds.
In the face of COVID, dozens of states collectively lost tens of billions of dollars at the hands of identity thieves impersonating out-of-work Americans seeking unemployment insurance. Some 30 states and 10 federal agencies now use ID.me to screen for ID thieves applying for benefits in someone else’s name.
But ID.me has been problematic for many legitimate applicants who saw benefits denied or delayed because they couldn’t complete ID.me’s verification process. Critics charged the IRS’s plan would unfairly disadvantage people with disabilities or limited access to technology or Internet, and that facial recognition systems tend to be less accurate for people with darker skin.
Many readers were aghast that the IRS would ask people to hand over their biometric and personal data to a private company that begin in 2010 as a way to help veterans, teachers and other public servants qualify for retail discounts. These readers had reasonable questions: Who has (or will have) access to this data? Why should it be stored indefinitely (post-verification)? What happens if ID.me gets breached?
The Washington Post reported today that in a meeting with lawmakers, IRS officials said they were considering another identity verification option that wouldn’t use facial recognition. At the same time, Senate Finance Committee Chairman Ron Wyden (D-Ore.) challenged the Treasury Department and IRS to reconsider the biometric requirements.
In a statement published today, the IRS said it was transitioning away from using a third-party service for facial recognition to help authenticate people creating new online accounts.
“The transition will occur over the coming weeks in order to prevent larger disruptions to taxpayers during filing season,” the IRS said. “During the transition, the IRS will quickly develop and bring online an additional authentication process that does not involve facial recognition. The IRS will also continue to work with its cross-government partners to develop authentication methods that protect taxpayer data and ensure broad access to online tools.”
“The IRS takes taxpayer privacy and security seriously, and we understand the concerns that have been raised,” IRS Commissioner Chuck Rettig wrote. “Everyone should feel comfortable with how their personal information is secured, and we are quickly pursuing short-term options that do not involve facial recognition.”
The statement further stressed that the transition announced today does not interfere with the taxpayer’s ability to file their return or pay taxes owed. “During this period, the IRS will continue to accept tax filings, and it has no other impact on the current tax season,” the IRS said. “People should continue to file their taxes as they normally would.”
It remains unclear what other service or method the IRS will use going forward to validate the identities of new account signups. Wyden and others have urged the IRS to use Login.gov, a single sign-on service that Congress required federal agencies to use in 2015.
“Login.gov is already used to access 200 websites run by 28 Federal agencies and over 40 million Americans have accounts,” Wyden wrote in a letter to the IRS today. “Unfortunately, login.gov has not yet reached its full potential, in part because many agencies have flouted the Congressional mandate that they use it, and because successive Administrations have failed to prioritize digital identity. The cost of this inaction has been billions of dollars in fraud, which has in turn fueled a black market for stolen personal data, and enabled companies like ID.me to commercialize what should be a core government service.”
Login.gov is run by the U.S. General Services Administration, which told The Post that it was “committed to not deploying facial recognition…or any other emerging technology for use with government benefits and services until a rigorous review has given us confidence that we can do so equitably and without causing harm to vulnerable populations.”